BATCH 5
Professional Certificate Programme in Cybersecurity and AI
Taught by IITM Pravartak guest faculty | Gain expertise in offensive, defensive and AI-driven cybersecurity
Avail Early Enrolment Benefit by Enrolling Before Invalid liquid data
Application Fees: ₹1200 + GST
Become a Cybersecurity Expert with IITM Pravartak Faculty and Industry-Aligned Trainings

Become an AI-Ready Cybersecurity Professional with IITM Pravartak
Where AI and ML evolve, cybersecurity stands as their ultimate challenge—a domain where intelligence meets vigilance. In an age of rapid digital transformation, the call for AI-powered cybersecurity expertise grows louder. With India’s bold initiatives, such as 5G, smart cities projects, API Setu, Make in India and Digital India, the future belongs to those who can master this intricate field of innovation and security.
75%
3x
18.33%
Programme Overview
The Professional Certificate Programme in Cybersecurity and AI by IITM Pravartak is designed for professionals aiming to build deep, practical expertise in both offensive and defensive cybersecurity, while gaining in-demand skills in AI-driven cybersecurity practices.
This 3-in-1 programme includes:
Certification from IITM Pravartak - the technology innovation hub of IIT Madras
CISSP training for leadership roles in cybersecurity
3 IBM certificates on GenAI, Encryption and Forensics
The programme is led by Prof. Noor Mohammed, cybersecurity guest faculty at IITM Pravartak and features select live masterclasses, and weekly recorded lectures, complemented by domain expert-led live sessions that deepen your understanding of advanced cybersecurity concepts, tools, and real-world applications.
Note:
A few weeks including CISSP training and offensive cybersecurity fundamentals are taught by domain experts only.
Programme Highlights
Led by IITM Pravartak Guest Faculty
Taught by Prof. Noor M, cybersecurity expert and guest faculty

IITMP Guest Faculty Pedagogy
Select live masterclasses and weekly recorded videos by IITM Pravartak guest faculty*
Global Cybersecurity Training
CISSP training by domain experts
IBM Industry Certification
Get industry-ready with 3 IBM certificates on GenAI, Encryption, and Forensics

AI in Cybersecurity
AI- driven modules on anomaly detection, adversarial defense, and more

Domain Expert (DE) Sessions
Weekly live sessions (including doubt solving) covering key concepts & hands-on applications
IITM Research Park Immersion
Two-day campus immersion event at IIT Madras Research Park (Optional)

10+ Cutting-Edge Tools
Get hands on learning with OpenVAS, Nessus, Wireshark, SQLMap, and more tools

Study of Global Frameworks
Learn about frameworks like GDPR, ISO 27017, and more
Capstone Project
Solve complex industry problems through a comprehensive capstone project

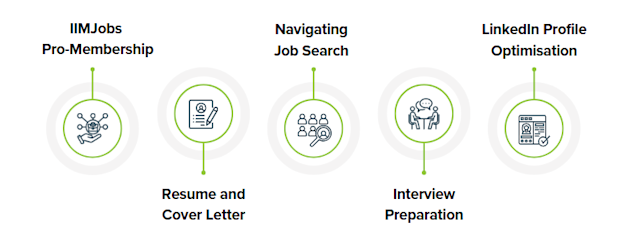
Career Services Support
Six-months IIMJobs Pro membership, resume builder, and career preparation
Note:
All programme highlights stated in this section and across the programme are subject to change at the discretion of IITM Pravartak and Emeritus.
Only participants who have successfully completed the programme will be allowed to visit the IITM Research Park.
Overall, 50% attendance in both domain-expert led live sessions and live faculty masterclasses are required to achieve programme completion.
A few weeks including CISSP training and offensive cybersecurity fundamentals are taught by domain experts only.
The immersion will only be conducted with a minimum number of learners signing up.
Domain expert is the programme leader responsible for conducting weekly live sessions.
*Schedule for faculty masterclass will be shared post programme orientation.
Learn AI and ML From Renowned IITM Pravartak Guest Faculty

Guest Faculty, IITM Pravartak
- Ph.D. Degree in Computer Science and Engineering from IIT Madras
- M.Tech. Degree in Electronics Design Technology from National Institute of Electronics and Information Tec...
Train for the Gold-Standard CISSP Certification
Recognised globally, the Certified Information Systems Security Professional (CISSP) is one of the most prestigious and respected certifications in cybersecurity. It affirms a professional’s expertise in designing, implementing, and managing secure business environments—making it essential for those aiming for leadership roles such as Security Architect, Cybersecurity Manager, or Chief Information Security Officer (CISO). CISSP is frequently listed as a preferred or mandatory requirement in job postings for senior cybersecurity positions by top employers, including Google, Accenture, and Deloitte.
175K+
35%
$120K
How This Programme Gives You the Edge
Professional Certificate Programme in Cybersecurity and AI by IITM Pravartak | Other Outdated/Non-Accredited Technical Certificate Programmes | |
|---|---|---|
Certification from a Top Ranked Institution | Certification from IITM Pravartak, which is the technology innovatrion hub of a leading engineering institute | Certification from non-accredited or low-ranked institutes |
IITM Pravartak Faculty-Led Teaching | Select live masterclasses and weekly recorded videos by Prof. Noor Mahammad SK, presenting learners with an opportunity to learn directly from IITM Pravartak guest faculty | Limited involvement from institute faculty |
Depth of Cybersecurity and AI Topics | Emphasis on technical foundations with hands-on training, exploring case studies in cybersecurity alongside AI-driven anomaly detection, adversarial defence, and SOC automation using industry-standard tools. | Programmes are designed with a narrow scope and their technical depth is low to moderate at best |
Professional Industry Certification Training | Prestigious CISSP certification training is part of the curriculum | Rarely offered additional certificate trainings that often come with additional costs |
Professional IBM Certification | Three IBM professional certifications that instantly add credibility to your resume | Additional certifications are rarely offered and come with add-on costs |
Tools and Libraries | Get access to more than 10 most in-demand tools, such as Nmap, Metasploit, SEToolkit, OpenVAS, Nessus, Wireshark, SQLMap, and more. | Curricula covering fewer and outdated tools, with no access to masterclasses and little guidance from domain experts/faculty |
Who is this Programme for?
This programme is designed for professionals who are looking to battle growing security threats in an increasingly digital landscape while building a lucrative career in the field with strong AI expertise. If you are a technical professional looking to deepen your expertise, this programme is tailored to your needs.
Specifically, this programme is ideal for:
Seasoned IT and Tech Professionals: System administrators, network engineers, and IT support experts looking to specialise in cybersecurity.
Administrators and Support Professionals: Organisation personnel tasked with securing and maintaining IT infrastructure.
Product Owners and Consultants: IT professionals seeking cybersecurity knowledge.
Aspiring Cybersecurity Enthusiasts: Individuals who are looking to start or transition into a cybersecurity career and want a structured entry.
By the end of this programme, you'll be equipped to:
Implement and drive cybersecurity technologies
Showcase hands-on applications of advanced tools and frameworks
Transition towards mainstream cybersecurity roles at pace
Elevate your cybersecurity skills with AI
Eligibility criteria for this programme:
Minimum Graduate; Diploma Holders with min. 5 years of work experience
Programme Modules
Introduction to Operating Systems and System Architecture
Virtual Memory: Paging, Segmentation, and Configuration
File Systems: FAT, NTFS, ext3/4 and File Management
Understanding and Managing File Permissions (Windows and Linux)
User Mode vs. Kernel Mode and Privilege Levels
PowerShell and Bash: Commands and Scripting
Introduction to Virtualisation and Setting Up Kali Linux
[Taught by IIT Faculty and Domain Experts]
Introduction to Networking and Network Topologies
Network Devices: NIC, Hub, Switch, Router and Repeater
OSI and TCP/IP Model: Comparison and Implementation
IP Addressing: IPv4, IPv6 and Subnetting
Network Protocols: DNS, TCP, UDP, ARP, ICMP
Packet Analysis with Wireshark (TCP, UDP, ARP)
WLAN Security and Wireless Encryption (WEP, WPA, WPA2, WPA3)
[Taught by IIT Faculty and Domain Experts]
Cyber Intelligence and Reconnaissance
Threat Enumeration and Cyber Risk Management
Exploitation and Network Attack Strategies
Phishing, Social Engineering, and Malware
DoS Exploits and Secure Session Management
[Taught by Domain Experts]
Firewall Evasion and Web Server Security
Web Application Security and Exploitation
Wireless, Mobile, and IoT Security
Cryptography and Cloud Security
[Taught by Domain Experts]
Security and Risk Management
Asset Security
Security Architecture and Engineering
Communication and Network Security
Identity and Access Management (IAM)
Security Assessment and Testing
Security Operations
Software Development Security
[Taught by Domain Experts]
Deep Learning and NLP for Cybersecurity
AI-Driven Anomaly and Malware Detection Techniques
User Behavior Analytics (UEBA) and Insider Threat Detection
Adversarial Attacks and Model Robustness in AI Systems
AI Integration with SIEM and SOAR for Automated Threat Response
MITRE ATT&CK Framework for Threat Hunting
Ethics, Bias, and Governance in AI Security
[Taught by IIT Faculty and Domain Experts]
An introduction to Cloud Security
Identity and Access Management (IAM) in the Cloud
Cloud Data Security and Encryption
Cloud Security Monitoring and Incident Response
Securing Cloud Applications and Workloads
[Taught by IIT Faculty and Domain Experts]
An introduction to SOC and Threat Monitoring
Incident Response and Threat Hunting
[Taught by IIT Faculty and Domain Experts]
Introduction to Digital Forensics
Digital Evidence Collection and Analysis
Network and Log Forensics
Malware Memory Forensics
Mobile and Cloud Forensics
[Taught by IIT Faculty and Domain Experts]
The capstone project is a comprehensive, real-world assignment in which participants apply their knowledge and skills to solve industry-specific problems
It integrates concepts from their coursework, encouraging critical thinking and innovation
Capstone projects help participants gain hands-on experience, making them industry ready by demonstrating their ability to tackle complex challenges in a professional setting
Note:
All programme curriculum is subject to change as per the discretion of IITM Pravartak or Emeritus.
The programme curriculum consists of content from both IIT Madras Guest faculty and domain experts. 60% of the pre-recorded content is taught by the faculty and the rest is taught by the domain experts.
Live sessions are held on weekends. CISSP training includes sessions on both Saturday and Sunday, with most content delivered live.
Gain Credentials from IBM, a Pioneer in Cybersecurity and AI Technology
Get Started with Generative AI in Cybersecurity
SIEM and SOC Tasks Using Generative AI
Final Project and Exam
Introduction to encryption
The Quantum era and Quantum computers
Safeguard your data with Quantum-safe cryptography
IBM’s Quantum-safe solution
Final Quiz
Incident Response Fundamentals
Digital Forensics and Investigation
Final project
System Requirements to Pursue the Programme
Personal laptop/desktop with Windows 10/11 (64-bit) or Ubuntu 20.04+, VMware Workstation (Free), minimum 12 GB RAM (16 GB recommended), 4-core Intel i5/i7 or AMD equivalent, and 120 GB free SSD storage.
Note:
Learners must have a personal system meeting minimum hardware and virtualization requirements to run hands-on labs. Company-issued, restricted, or low-spec devices (e.g., 8 GB RAM) may not support all lab activities.
Programme FAQs
The Professional Certificate Programme in Cybersecurity and AI by IITM Pravartak equips learners with deep technical knowledge in cybersecurity and artificial intelligence. It offers cybersecurity course training, hands-on labs with 10+ tools, and prepares students for global certifications like CISSP and 3 IBM industry certificates for higher industry-readiness.
Yes, the programme includes CISSP training aligned with ISC2 standards to help you prepare for the certification. (Please note: the certification exam voucher is not included.)
CISSP certification focuses on advanced cybersecurity leadership. This programme provides CISSP-aligned training to help you build a strong foundation for senior cybersecurity roles.
The CISSP training is included in the programme fee. Learners receive comprehensive preparation through live sessions. (Please note: the CISSP exam fee is not included and must be paid separately to ISC2. )
The course includes a dedicated module on AI in Cybersecurity, providing hands-on experience with AI-driven cybersecurity solutions. Completing the programme also adds to your credentials for artificial intelligence certification and AI certification programmes.
Anyone with a graduate degree (10+2+3) or diploma with minimum 5 years of experience can apply. The course is ideal for professionals with more than 5 years of experience looking for cybersecurity certification training aiming for standards like CISSP.
Yes. Participants will be trained for global cybersecurity certifications, including the ISC2 CISSP certification. The curriculum aligns with ISC2 certifications, making your skills recognised worldwide.
Yes, this programme integrates AI certification programs by teaching AI's application in cybersecurity. This dual focus on cybersecurity and AI ensures that you gain interdisciplinary skills highly valued in today’s job market.
After completion, participants gain access to Emeritus Career Services, including an IIMJobs Pro membership. You will be well-positioned to earn roles requiring cybersecurity professional certificate credentials or transition into cybersecurity certifications for beginners' pathways.
Early registrations are encouraged. Seats fill up quickly!
Flexible payment options available.
Starts On